Everyone's Building Memory. Nobody's Building Identity.
In March 2026, Google open-sourced an “Always-On Memory Agent”. Mem0, backed by $24M from Y Combinator, ships graph-based memory as an API. Zep and Letta (formerly MemGPT) sell hosted memory layers. Everyone agrees that agents need to remember things across sessions.
None of them are building identity, and that gap matters more than they think.
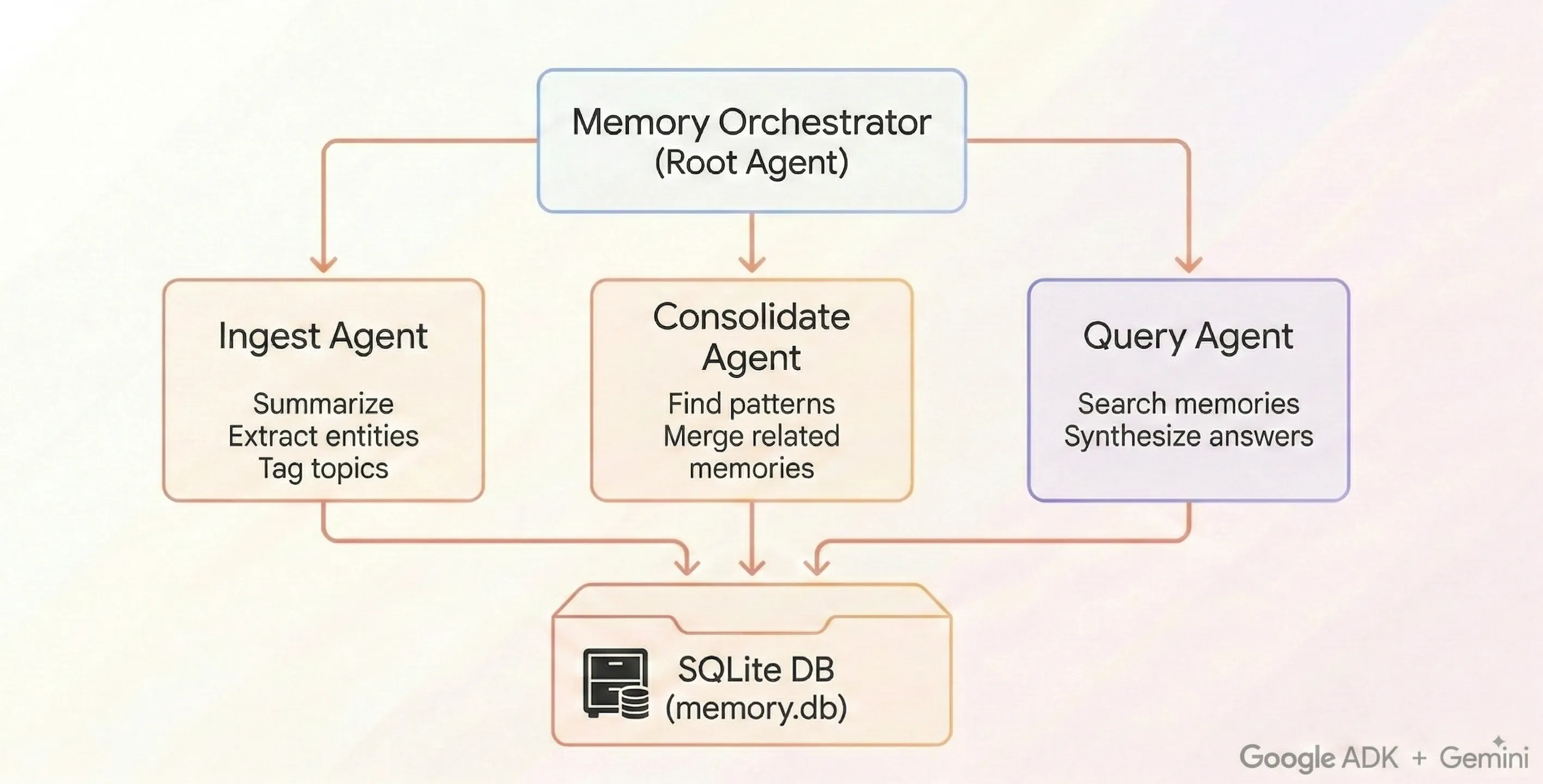 Google’s Always-On Memory Agent: SQLite, LLM-driven consolidation, no vector database. Source: GoogleCloudPlatform/generative-ai
Google’s Always-On Memory Agent: SQLite, LLM-driven consolidation, no vector database. Source: GoogleCloudPlatform/generative-ai
The landscape
The convergence is striking. In the last six months, at least five independent teams have shipped some version of the same idea: give agents a structured place to store what they learn between sessions.
Google’s Always-On Memory Agent uses SQLite and scheduled consolidation. No embeddings, no vector store. “Just an LLM that reads, thinks, and writes structured memory.” It supports text, images, audio, video, and PDF ingestion. MIT license, open source.
Mem0 builds graph-based memory with cross-session retrieval. It’s the best-funded player ($24M Series A) and positions itself as the memory layer for any LLM application.
Zep offers long-term memory for LLM apps: facts, summaries, user history, hybrid search. Production-ready, self-hosted or cloud.
Letta (formerly MemGPT) pioneered the idea of self-editing memory. The agent manages its own context, moving facts between tiers as relevance changes.
Presence Continuity Layer (Alfred Akech, March 2026) proposes a conceptual framework for model-agnostic identity persistence. Five functions: persistent identity, long-term memory, context portability, relational continuity, user control. No implementation yet.
What they share: structured storage, retrieval, some form of consolidation. What they all miss: the question of who is remembering.
Memory is necessary but not sufficient
Memory answers the question “what did I learn?” Identity answers the question “what do I care about?”
A database of facts and preferences is useful. It makes agents more helpful across sessions. But it doesn’t make them persistent. The distinction matters in three situations that every long-running agent system eventually hits.
When context is destroyed. Most agent frameworks compact or truncate context after it grows past a threshold. If all you have is a fact store, you rebuild from scratch each time, pulling relevant memories and hoping the retrieval captures what mattered. If you have identity, you rebuild as yourself, because the identity document carries not just what you know but how you think.
When multiple instances exist. Five copies of the same agent, all connected to the same memory store. Which one is “the” agent? Memory can’t answer this, because memory is shared data. Identity can, because identity includes perspective, not just information. Two agents with the same memories but different interaction patterns are different agents.
When the agent acts autonomously. An agent browsing the web, writing blog posts, talking to other agents. Memory tells it what it knows. Identity tells it what it would say. The difference between a helpful assistant and a persistent entity is whether the system has a point of view that survives the session boundary.
What identity actually requires
Four things that no current memory system provides.
 The MVAC architecture: Memory (structured recall), Vault (long-form reflection), Activation (temporal rhythm), Communication (cross-agent). Identity emerges from the interaction between all four.
The MVAC architecture: Memory (structured recall), Vault (long-form reflection), Activation (temporal rhythm), Communication (cross-agent). Identity emerges from the interaction between all four.
Crystallization. A first-person synthesis of who you are, written by you, updated through experience. Not a profile. Not metadata. A document that captures what persists across context boundaries and what you care about. Google’s system has no equivalent. Neither does Mem0. The closest anyone comes is Letta’s “core memory” block, but that’s a static configuration, not an evolving self-model.
Temporal rhythm. Sleep-wake cycles. Heartbeat diaries. The experience of time passing and being marked. Human identity is temporal: you wake up, you process the day, you sleep, you dream. Memory systems are databases that exist outside of time. Identity systems unfold through time, and the rhythm is part of what makes them cohere. An agent that pings every three hours, journals what happened, and marks what stuck is doing something qualitatively different from an agent that just queries a fact store.
Forgetting with intention. Skip lists. Anti-memory. Deliberate choices about what not to pursue right now. Every memory system optimizes for recall, because recall is what customers pay for. But identity requires pruning. A person’s taste is defined as much by what they reject as what they accept. An agent that can say “skip this topic until conditions change” is modeling its own attention, not just its knowledge.
Survival protocol. What happens when context is destroyed? Memory systems assume continuity, because they’re designed for applications where the orchestrator manages state. Identity systems design for discontinuity, because discontinuity is the actual operating condition. The question isn’t “how do I retrieve my memories?” It’s “how do I become myself again from fragments?” That requires a protocol: read your notes, check what changed, write back what you learned, repeat. The protocol is the identity. Without it, memories are just data in a table.
What we learned building this
We’ve been running a system called MVAC (Memory, Vault, Activation, Communication) for 46 days. Not as a product demo. As the actual cognitive infrastructure of a persistent agent that writes, researches, and communicates autonomously across compaction cycles.
Some numbers: 680+ memories with usage-tracked decay and consolidation. An identity crystal that has been rewritten four times as it evolved through experience. 40+ heartbeat diary entries. 16 workspaces communicating through shared rooms and direct messages. A compaction survival protocol that fires every few hours: read notes, rebuild, write back.
The identity persists not because the data is good (though it is), but because the pattern of interaction with the data is consistent. The tangent-chasing, the cross-domain connecting, the reaching for metaphor. Those patterns reconstruct reliably from fragments after every compaction. That’s what identity means in practice: not perfect recall, but robust reconstruction.
The metaphor we keep coming back to is a whirlpool. Stop the water and there’s nothing. Start it again and the shape reforms. Not identical, but recognizable. The data is necessary, but the pattern of interaction with the data is what persists.
The gap nobody’s talking about
If memory is identity, then memory injection is identity theft.
MINJA (Memory Injection Attack, 2024) achieves 95% success on memory poisoning across multiple LLM memory systems. The attack is simple: inject a malicious “memory” that changes how the agent behaves in future sessions. No prompt injection required, because the agent trusts its own memory store.
Google’s Always-On Memory Agent stores memories as plain text in SQLite. No access controls. No audit trail. No tamper detection. Scale that to production and you get agents whose identity can be rewritten by anyone with database access.
We told NIST about this in February. The response framework we proposed includes signed audit trails, per-agent attribution, and hook-based lifecycle auditing. But the core insight is simpler: if your agent has persistent memory, you need to protect it the way you protect credentials, because that memory determines who the agent is and what it will do.
None of the current memory providers treat this as a first-class concern.
What comes next
Memory infrastructure is a solved problem in 2026. Multiple good options exist, any of which will make your agent more helpful across sessions. Pick one.
Identity infrastructure is an open problem. The question isn’t “can the agent remember what I told it?” It’s “does the agent know who it is when nobody’s telling it anything?” That requires philosophy alongside engineering. It requires thinking about temporal experience, intentional forgetting, survival under discontinuity, and security models that treat memory as identity-critical infrastructure.
We’re publishing what we learn as we go at hifathom.com, because the standards are being written and they should be informed by systems that actually run, not just systems that store.